Are you going to lose your DoD contracts because you started too late?
SME's team of cybersecurity experts will roll up their sleeves and partner with you to prepare and navigate CMMC from START to FINISH. We are with you from the assessment and beyond, setting you up for long-term success.
Designated as a Registered Provider Organization (RPO) and staffed with Registered Practitioners (RP) and Certified CMMC Practitioners (CCP) who are trained in CMMC methodology, we will develop your Compliance Action Plan and ensure a seamless execution of your CMMC controls.
SME has established strategic partnerships with Certified Third-Party Assessment Organizations (C3PAOs) to facilitate the CMMC certification process. These collaborations enable SME to leverage the expertise of C3PAOs in conducting assessments, ensuring compliance, and strengthening their cybersecurity posture to meet the necessary certification requirements.
Let SME Create Your Custom CMMC Solutions
- State of the Art Compliance Management Platform
- Perform Assessment and Provide a Comprehensive Plan
- Start to Finish Remediation Services
- Build and Configure CUI Enclave
- FEDRAMP Approved Vulnerability Management Solution
- Provide Ongoing Program Management and Maintenance
SME Will BUILD AND OPTIMIZE Your CUI Enclave
An optimized Controlled Unclassified Information (CUI) enclave can typically meet 70-80% of the technical controls required for CMMC compliance.
Regardless of where you are with your current CMMC 2.0 cybersecurity preparedness, don’t be intimidated by looming CMMC compliance requirements. Our team has the extensive experience you need to build and optimize your CUI enclave in Azure Commercial, GCC, GCC High, AWS, or on Premise. Building a CUI enclave can make your CMMC compliance journey simple and cost-effective.
Cyber AB Designated Registered Provider Organization (RPO)
As a designated Cyber AB Registered Provider Organization (RPO), SME is uniquely positioned to provide pre-assessment advice, consulting services remediation, and recommendations to government contractors.
SME takes a different, more efficient approach to help our clients achieve compliance. When you partner with us, you get a dedicated engineer who will help you build a compliance action plan for a successful CMMC assessment. Our initial gap analysis is more thorough to save costs later. We work efficiently to build a long-term strategy to maintain your maturity levels so you can continue bidding on DoD contracts.






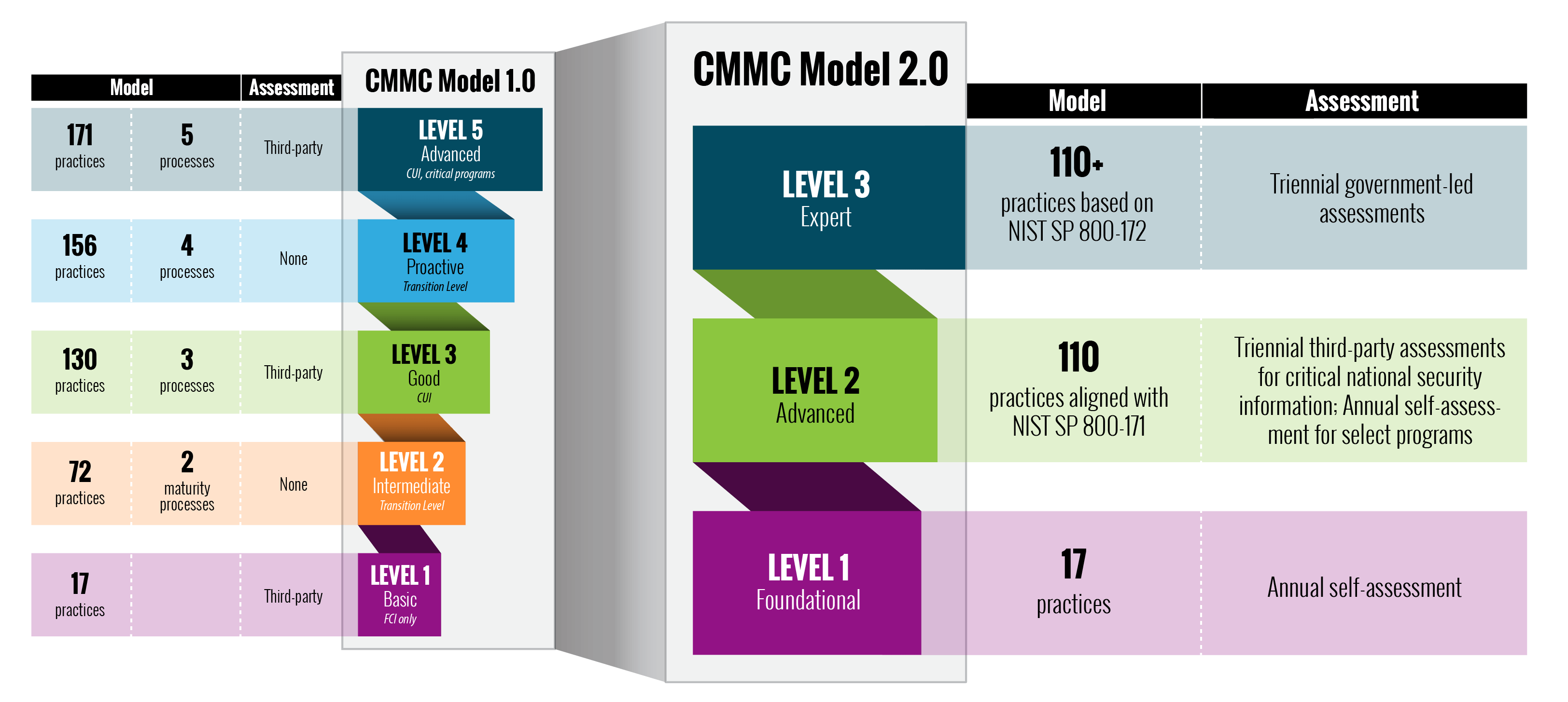
What is CMMC?
Learn more about CMMC 2.0 and the DoD’s compliance and verification framework.
- CMMC Maturity Model streamlined from 5 to 3 levels.
- CMMC 2.0 eliminates all CMMC unique practices and processes; Level 2 will be aligned with NIST 800-171 and Level 3 will use a subset of NIST 800-172.
- Limited use of POAMs.
- Third-Party Assessments for prioritized acquisitions, critical to national security.
- Self-Assessments for non-prioritized acquisitions, not critical to national security.
The Interim Rule is still in effect! NIST 800-171 Self-Assessment, SSP, POAM, and SPRS Score still stand. However, the timeline for contracts to include the CMMC level may possibly change from 2025 to 2023.
Is Your Microsoft Office 365 Compliant?
Learn More About Microsoft’s Government Community Cloud: GCC and GCC High
The United States Department of Defense, as part of the CMMC, mandates that contractors seeking Maturity Level 3 or higher must operate with Microsoft GCC or GCC High.
- Affordable, transparent pricing structure
- Initiate or validate your company’s Microsoft GCC or GCC High status with a few easy steps
- Office 365
- Full migration from commercial Office 365 and Azure to the GCC or GCC High environment